Description
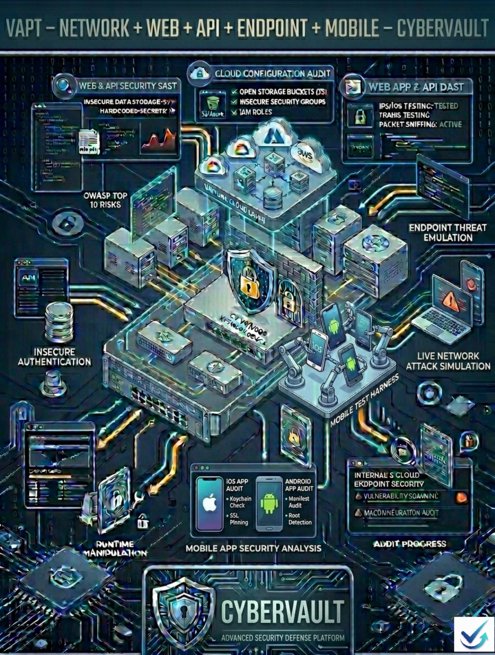
VAPT – Network + Web + API + Endpoint + Mobile
By Cybervault – Qualified & Independent Cybersecurity Auditors
Full Service Description
Vulnerability Assessment and Penetration Testing (VAPT) – Network + Web + API + Endpoint + Mobile is a comprehensive security assessment designed to identify, validate, and demonstrate exploitable vulnerabilities across an organization’s entire technology ecosystem.
Cybervault delivers independent, evidence-driven VAPT services through the Make Audit Easy platform, covering network infrastructure, web applications, APIs, endpoint systems, and mobile applications (Android & iOS).
Our assessment methodology is structured, risk-based, and aligned with internationally recognized frameworks and testing standards, including:
-
OWASP Top 10
-
OWASP API Security Top 10
-
OWASP Mobile Top 10
-
National Institute of Standards and Technology SP 800-115
The engagement combines advanced automated vulnerability scanning with controlled manual penetration techniques to simulate real-world attacker behavior across multiple attack surfaces. Each vulnerability is validated to eliminate false positives and prioritized based on severity, exploitability, regulatory exposure, and business impact.
Cybervault evaluates both internal and external threat vectors, authentication and authorization controls, API logic flaws, endpoint hardening posture, mobile application data security, encryption practices, and backend integrations. The objective is to uncover real attack paths, demonstrate potential business impact, and provide clear, actionable remediation guidance.
The engagement concludes with a detailed technical report and an executive summary, including risk-ranked findings, proof-of-concept evidence, and a prioritized remediation roadmap aligned to your business and compliance requirements.
| Parameter | Basic | Standard | Enterprise | Advance |
| Audit Mode | Virtual Only | Virtual Only | Virtual + Onsite | Virtual + Onsite |
| Network Assets (IPs / Devices) | Up to 5 | Up to 10 | Up to 20 | Up to 50 |
| Web Applications | 1 Website | 1 Website | 2 Websites | 3–4 Websites |
| Web Pages (per app) | Up to 5 | Up to 8 | Up to 12 | Up to 20–25 |
| API Endpoints | Up to 8 APIs | Up to 20 APIs | Up to 40 APIs | Up to 80–100 APIs |
| Endpoint Devices (Laptops / Desktops / Servers) | Up to 20 | Up to 50 | Up to 100 | Up to 300 |
| Mobile Applications (Android / iOS) | 1 App | 1 App | 2 Apps | 3–4 Apps |
| Mobile Testing Coverage | Basic security checks | Standard OWASP MASVS | Full MASVS (L1/L2) | MASVS + abuse cases |
| Endpoint OS Coverage | Windows only | Windows / Linux | Windows / Linux / macOS | All + hardened builds |
| Authentication Testing | Basic login | Standard auth | Full auth + RBAC | Complex role abuse |
| Authorization Testing | Very limited | Limited | Comprehensive | Extensive |
| Business Logic Testing | Minimal | Moderate | Standard industry depth | Deep & edge cases |
| Malware / EDR Evasion Checks | NA | Limited | Included | Advanced |
| Privilege Escalation Testing | NA | Limited | Included | Advanced |
| OWASP Coverage | OWASP Top 10 | OWASP Top 10 | OWASP + API + MASVS | OWASP + API + MASVS + Custom |
| Manual Exploitation | Minimal | Partial | Included | Extensive |
| False Positive Validation | Critical only | High & Critical | All severities | All severities |
| Add On | ||||
| Additional Network Asset | 10% | 7% | 7% | 5% |
| Additional Web Page | 10% | 7% | 5% | 5% |
| Additional API Endpoint | 10% | 7% | 5% | 5% |
| Additional Endpoint Device | 10% | 7% | 5% | 5% |
| Additional Mobile App | 15% | 10% | 7% | 5% |
| Onsite Testing (Same City) | NA | NA | 15% | 10% |
| Onsite Testing (Another City) | NA | NA | 20% | 15% |
| Timeline | ||||
| Audit Timeline | 3–11 Days | 5–11 Days | 10–20 Days | 15–30 Days |
| Post-Audit Support | 5 Months | 5 Months | 7 Months | 11 Months |
*TC
Key Testing Coverage
Network Security Testing
-
External & internal network assessment
-
Open ports & exposed services review
-
Firewall configuration & segmentation validation
-
Lateral movement simulation
-
Patch management & misconfiguration analysis
Web Application Security Testing
-
Injection vulnerabilities (SQLi, XSS, etc.)
-
Broken authentication & session management flaws
-
Access control weaknesses
-
Security misconfigurations
-
Business logic abuse testing
API Security Testing
-
Broken Object Level Authorization (BOLA)
-
Authentication & token mismanagement
-
Excessive data exposure
-
Rate limiting & abuse testing
-
Parameter tampering & mass assignment
Endpoint Security Testing
-
Operating system hardening review
-
Local privilege escalation testing
-
Weak credential policy assessment
-
Patch & update gap identification
-
Antivirus / EDR effectiveness validation
-
Persistence mechanism analysis
Mobile Application Security Testing (Android & iOS)
-
Insecure local data storage
-
Weak cryptographic implementations
-
Reverse engineering & code tampering risks
-
Certificate pinning validation
-
Insecure API communication
-
Authentication & session management flaws
-
Root/Jailbreak detection bypass testing
Who This Service Is For
-
SaaS & Product Companies
-
FinTech & Payment Platforms
-
E-commerce & Digital Businesses
-
Mobile application providers
-
Enterprises with distributed endpoints
-
Organizations preparing for ISO 27001, SOC 2, PCI DSS, RBI, SEBI, or IRDAI compliance
-
Businesses seeking independent security validation
Why Cybervault
-
Independent and objective cybersecurity assessments
-
Risk-based, compliance-aligned methodology
-
Hybrid manual + automated testing approach
-
Clear, developer-focused remediation guidance
-
Executive-level reporting aligned with business impact










Reviews
There are no reviews yet.